In today’s rapidly expanding digital landscape, protecting sensitive digital data has become crucial. The global cybersecurity market is projected to experience substantial growth, with estimates suggesting an increase from USD 217.9 billion to 345.4 billion by 2026. This surge in demand highlights the need for proficient professionals in ethical hacking. This article aims to provide insights into learning ethical hacking in 2024, outlining the necessary pathways and prerequisites for acquiring these skills. Also, it will focus on the importance of obtaining the CEH certification, explore various hacking tools, and discuss potential career prospects in this field.
Understanding Hacking
Hacking involves investigating various systems, networks, and applications to identify potential weaknesses and strengthen security measures. This process ranges from benign exploration, where individuals seek to understand and improve system integrity, to malicious intrusion, where unauthorized access and harm may occur.
Importance of Ethical Hacking
White-hat hackers can assume the mantle of frontline defenders against cyber threats. They act proactively to preempt potential breaches. They mitigate risks before they escalate into significant security incidents. They are instrumental in identifying vulnerabilities. They conduct comprehensive penetration tests and meticulously assess the robustness of digital defenses. They simulate real-world attack scenarios and explore system weaknesses. They provide invaluable insights into potential security gaps. This enables organizations to bolster their digital fortresses. Ethical hacking, often learned through ethical hacking training, uncovers vulnerabilities and advocates for robust security measures. Ethical hackers contribute to the preservation of user privacy and online safety. This fosters a climate of trust and reliability.
Prerequisites for Learning Hacking
Learning ethical hacking necessitates a skill set with technical proficiency It also requires you to have a strong ethical compass. Prior experience in IT or cybersecurity can provide a solid foundation. Possessing a keen aptitude for solving problems is vital in ethical hacking. The hackers are tasked with deciphering intricate security challenges. They also have to analyze system vulnerabilities. They devise innovative solutions to fortify digital defenses.
Prior certification in cybersecurity can provide a solid footing. Aspiring ethical hackers often pursue specialized training programs. This includes programs such as the Certified Ethical Hacker certificate. The CEH certification will provide you with an understanding of ethical hacking principles. This validates their proficiency in safeguarding digital assets.
Learning Path for Beginners
Having a clear learning plan is crucial for those aiming to become ethical hackers. Beginners should start by understanding basic concepts in networking and programming languages. This forms a strong foundation for further learning.
It is helpful to grasp how computer networks function in the beginning. It is also important to understand how different devices communicate with each other. Understanding operating systems is also crucial. This is because many hacking techniques rely on exploiting vulnerabilities within these systems.
Aspiring ethical hackers can progress to more specialized courses after covering the basics. One notable certification is the CEH certification. This certification is recognized in the industry.
The certification covers various topics. This includes penetration testing and ethical hacking methodologies. It also includes tools used by cybersecurity professionals. Learners gain practical experience in identifying vulnerabilities through lab work. They conduct security assessments as well to gain practical experience. They also implement effective countermeasures.
Essential Hacking Tools and Technologies
Ethical hackers require tools to identify weaknesses in a system. These tools aid in hacking. They can range from the initial reconnaissance to the post-exploitation analysis. Mastering these tools is essential for ethical hackers. Reconnaissance tools help ethical hackers gather information about the target system. Tools like Shodan are commonly used for network discovery. They allow hackers to identify open ports running on target systems. Exploitation frameworks such as Metasploit provide a comprehensive suite of tools. They provide payloads for exploiting known vulnerabilities in target systems.
Network analysis tools like Wireshark enable ethical hackers to analyze network traffic. Wireshark helps identify anomalous behavior. It also helps see the potential security threats within the network infrastructure by examining packet data. Password cracking tools assist ethical hackers in recovering passwords from encrypted files. These tools employ various techniques, including brute-force attacks. It also includes rainbow table attacks. These help crack passwords and gain unauthorized access to target accounts. Forensic tools like EnCase are used by ethical hackers. They use these to investigate security incidents.
Hands-On Practical Exercises
Practical experience is crucial for aspiring ethical hackers. Engaging in these exercises cultivates critical thinking. It provides familiarity with the tools used in cybersecurity scenarios. Vulnerability assessment labs offer practical opportunities to identify security vulnerabilities across diverse systems. These can range from web servers to network services. These exercises ultimately enhance their preparedness for the CEH certification and beyond.
Common Hacking Techniques and Strategies
Ethical hackers need to learn the common tricks used to enter computer systems. Hackers might trick people into giving them passwords through fake websites. They also use special programs to find weaknesses in computer systems. They then exploit them to gain access. Another thing hackers do is spread harmful software like viruses. They do this to steal data. Understanding how hackers operate helps ethical hackers find these weaknesses before bad things happen.
Legal and Ethical Considerations
Legal considerations are crucial in ethical hacking. Ethical hackers must follow rules to stay within legal boundaries. It’s important to get permission before hacking any system. It is vital to always respect privacy. Ethical hackers also need to be responsible when they find weaknesses in systems. They need to report them to the right people instead of exploiting them. Following these rules keeps ethical hacking safe, fair, and trustworthy.
Advanced Hacking Skills
Ethical hackers need to level up their skills to keep pace with evolving threats. They need to master advanced techniques like reverse engineering. They take apart software to understand how it works. Ethical hackers also need to understand cryptanalysis. This involves breaking codes and encryption methods to uncover hidden information. Learning threat-hunting techniques helps them proactively search for signs of malicious activity within systems.
Building a Career in Ethical Hacking
Ethical hacking presents various career opportunities. This includes roles in penetration testing and security consulting. It also includes incident response and research. Continuous learning and gaining practical experience are essential steps toward advancement for those pursuing ethical hacking. Providing expert security advice to organizations or conducting innovative research offers diverse pathways for growth. You can stay updated on emerging technologies and obtain relevant certifications, such as the CEH certification, to carve out successful careers in ethical hacking.
Staying Updated: Trends in Hacking
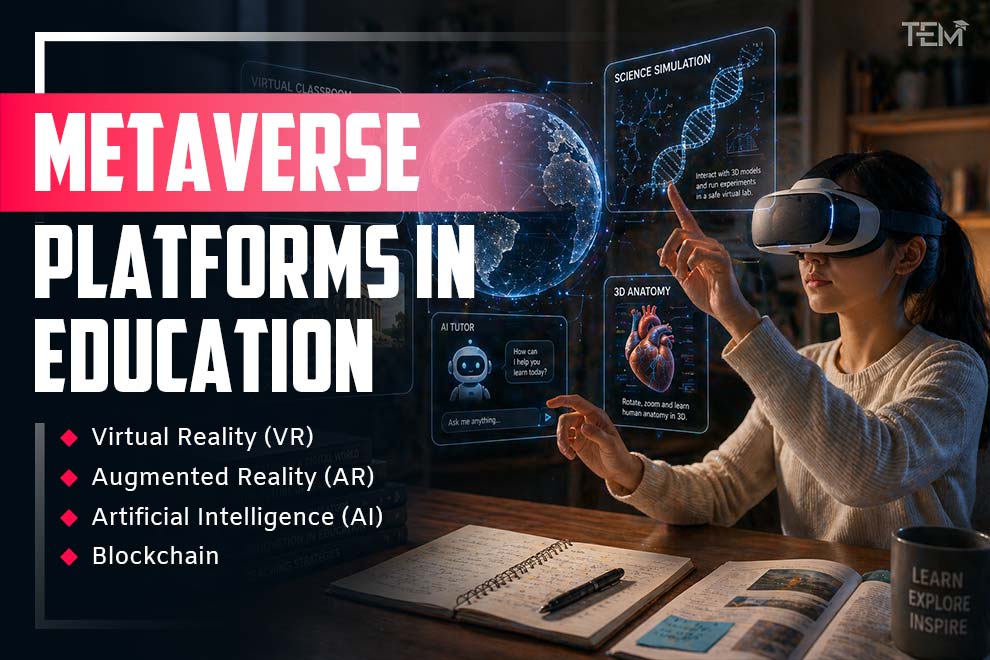
Hacking trends keep changing all the time because of new technologies. It is important to learn about what is happening in the cybersecurity world to stay updated. One trend is that hackers are targeting more Internet of Things devices as they become more common. This is creating new security problems. Another trend is that hackers are using artificial intelligence to make their attacks smarter and get around traditional security measures.
Challenges and Solutions
Ethical hacking faces challenges as cyber threats keep changing. Ethical hackers must work together and stay proactive to tackle these challenges. They must keep learning and adapting to new threats. One big challenge is that technology is always changing, and new weaknesses can appear quickly. Many types of cyber threats trick people into giving away information. Ethical hackers need to share information and work as a team to solve these challenges. They should always be using the latest tools to protect against cyber threats.
Community and Networking
The cybersecurity community serves as a nexus of knowledge sharing and mentorship. Engaging in forums and contributing to open-source projects cultivates a supportive network. It also fosters professional growth.
Conclusion
Mastering the art of hacking entails a journey of continuous learning and technical proficiency. Aspiring ethical hackers can embark on a rewarding career path by safeguarding digital assets and upholding the principles of security with the right blend of education and experience. Certifications like the CEH certification can bolster this. It validates their knowledge of ethical hacking practices. Ethical hackers are vital in safeguarding digital ecosystems and mitigating emerging threats by staying dedicated to upholding cybersecurity standards and embracing ongoing professional development.
FAQs
- Is it legal to learn hacking?
Learning hacking itself is legal, but it’s essential to abide by legal boundaries.
- What are the essential skills of an ethical hacker?
Essential skills for an ethical hacker include proficiency in networking and operating systems. It also requires knowing about programming languages and ethical decision-making.
- Can anyone become an ethical hacker, or is a specific background required?
Anyone with a passion for learning and ethical integrity can become an ethical hacker
Also Read: SANS Presents Cyber Security Training Event in San Francisco